Recently there has been some questions on the forums and Twitter as to how to mount forensic disk images that were captured from Mac system that implemented 4k block sizes. A few years ago, Mac systems started to use 4k blocks instead of 512 byte block sizes. This has caused some issues where you need to mount the image to do analysis without a major forensic suite. BlackBag wrote a good blog article on this last month however I hope to expand on it just a bit to include E01 files and FileVault encryption scenarios.
- Linux Mount Encrypted Dmg File
- Linux Mount Encrypted Dmg Download
- Linux Mount Encrypted Dmg Converter
- Linux Mount Encrypted Dmg Files
Option 1: Mount the DMG. If the Linux distribution you’re on has HFS support in the kernel (Ubuntu 14.04.1 LTS supports it), it’s pretty easy to just mount the DMG image: We’re using “sudo” because we need root privileges to mount things. The HFS+ file system type is specified with “-t hfsplus”. Mount Encrypted Dmg On Windows 6. Step 1: Download the DMG file and then convert it to ISO using a free online conversion service like YouConvertIt. Step 2: Once you do this, you can use another utility like ISO Editor to burn the ISO file to a USB drive. Remember, even if you convert the DMG to ISO, it's still Mac-compatible only, so you can't. Note: this technique can be used from a local Terminal window or a remote SSH connection. Mount the disk image. The first step is to mount (or attach) the disk image. From the command line, use: hdiutil mount cotvnc-20b4.dmg. Sep 25, 2012 Mounting DMG with hdiutil command. In order to manually mount DMG file, you'll need to use hdiutil command.
I will also detail how to mount the forensic disk images using newer APFS file system so analysts can start to do their thing while all the forensic tools catch up! APFS disk images already appear to use 4k block sizes as the default, at least on all my test systems. If you see otherwise, please let me know!
This article will try to provide some options to mount these images, however it cannot solve all the issues or combinations of disks/block sizes/host operating systems – it seems that you will have to upgrade to 10.13 at some point to solve many of these problems.
The following steps will bring you from a full HFS+ FileVault 4k disk image in EWF format to a mounted image using macOS 10.13. (If you have a raw (non-EWF) image, you can bypass steps 1 and 3.)
$ sudo mkdir /Volumes/4k_image/
$ sudo mkdir /Volumes/4k_mounted/
$ sudo xmount --in ewf --out dmg 4k.E01 /Volumes/4k_image/
$ hdiutil attach –nomount –blocksize 4096 /Volumes/4k_image/4k.dmg
[Input Password in Prompt Window]
$ diskutil cs list
$ sudo mount_hfs –o rdonly,noexec,noowners /dev/disk# /Volumes/4k_mounted/
1. Create a mount point to put the xmount converted DMG image (converted from EWF format). [sudo is required when dealing with /Volumes/ since 10.12]
2. Create another mount point to put the mounted image on. This will act as the root volume for the mounted image.
3. Using xmount (sudo required) to convert from EWF (--in) to DMG (--out) format. DMG is selected here since it is very Mac friendly. Provide the E01 image (use E?? if using segments) and the converted image mount point created in Step 1. This could take a few seconds if the disk image is large. Theoretically you can use another mounting utility, I've tried ewfmount on 10.13 and ran into errors that I'm still investigating. Having trouble installing Xmount? Does it say OS X Fuse is not installed? Look in the comments section for a fix.
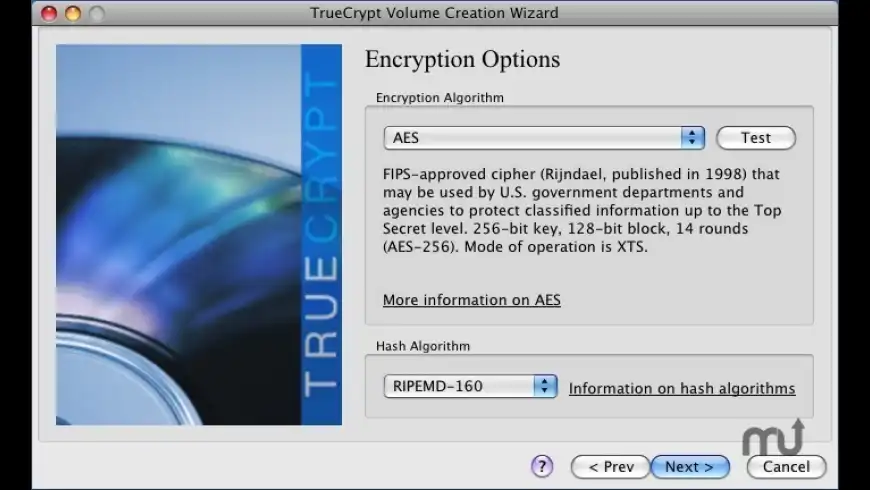
4. Using hdiutil, attach (but don’t yet mount) the DMG file created in Step 3. Using the hidden argument –blocksize we can specify 4096 (‘4k’ can also be used here). It is worth noting here that while hidden in 10.13 this option does not appear to exist in 10.12 versions of this utility. It is also is not detailed in the hdiutil man page. Gotta love hidden functionality! This will output a bunch of /dev/disk* options, however none of these are the ones you need thanks to CoreStorage.
5. If the image is FileVault encrypted a password window will appear, please put the password for the disk in here so it can be unlocked.
- If you want to do this all via the command line (you rock!) you can pass –stdinpass to the hdiutil command in Step 4 where it will prompt you for the password.
- You will then need to use ‘diskutil cs unlockVolume <LogicalVolumeGUID> ‘ after determining the Logical Volume GUID to use by using ‘diskutil cs list’. (Similar to Step 6) Note the Lock Status highlighted in the screenshots below.
6. Next use ‘diskutil cs list’ to determine which disk to using in Step 7. Determine which volume you will be performing analysis on, in the screenshot above it is /dev/disk6.

7. Using mount_hfs (with sudo again) we can mount /dev/disk6 (the ‘#’ is just a variable used above, yours may be a different number) using a variety of options (you can choose your own, however I normally use read only, ignore ownership, and limit binary execution options. Also provide it the second mount point you created in Step 2.
Linux Mount Encrypted Dmg File
If it all works out, congrats you now have a mounted image!
A similar approach can be used for new APFS disk images. Anyone who has tried to capture their disk images in 10.13 might have had a problem doing so due to System Integrity Protection (SIP). SIP is now protecting /dev and will likely make forensic acquisition and analysis more difficult if you happen to interact with /dev often. Easy fix – disable SIP. While not technically good for security purposes, it can be a general pain in the posterior to have on. To disable it, reboot into Recovery mode, open the Terminal and type ‘csrutil disable’ and restart the system. Yes, you can re-enable it later with ‘csrutil enable’.
- $ sudo mkdir /Volumes/apfs_image/
- $ sudo mkdir /Volumes/apfs_mounted/
- $ sudo xmount --in ewf --out dmg apfs.E01 /Volumes/apfs_image/
- $ hdiutil attach –nomount /Volumes/apfs_image/apfs.dmg
- $ diskutil ap list
- $ diskutil ap unlockVolume <Disk GUID> –nomount
- $ sudo mount_apfs –o rdonly,noexec,noowners /dev/disk# /Volumes/apfs_mounted/
Because it is so similar to the process above, my description of each step here will be limited. In Step 4 we do not need to use –blocksize as it just happens to work without it. In Step 5, instead of ‘diskutil cs list’ we use ‘diskutil ap list’ – APFS does not use CoreStorage (cs) and instead uses APFS containerization (ap). The ‘ap’ will also be used in Step 6. Step 7 uses mount_apfs instead of mount_hfs for obvious reasons and would be used on /dev/disk6s1 as shown in the example screenshot below.
A big thanks to Ed and a “little birdy” for sanity checks and help!
The Macintosh Disk Image files which are otherwise known as DMG images are ISO image equivalent for Apple's Macintos operating systems. The DMG images have a different filesystem called the HFS. In this article we will tell you how to mount dmg images in Linux.

Linux Mount Encrypted Dmg Download
You can use the following command in a Terminal to mount the dmg image:
This command will mount a dmg image called filename.dmg in a folder named /media/iso. In case you get an error you can use the hfsplus option instead of the hfs option as shown below. This one also will have similar mounting effects and is generally applicable to newer dmg image files.
Linux Mount Encrypted Dmg Converter
The above two commands may not work correctly if you do not have proper support installed on your system for reading hfs or hfsplus. Generally this wont happen, so you need not worry. Some times the dmg file may not be a true dmg image instead it may be a zipped image. You can use the file command to check whether the dmg image you are trying to mount is an actual dmg image or not.